HackTheBox Challenge - Flag Command
Description
Embark on the “Dimensional Escape Quest” where you wake up in a mysterious forest maze that’s not quite of this world. Navigate singing squirrels, mischievous nymphs, and grumpy wizards in a whimsical labyrinth that may lead to otherworldly surprises. Will you conquer the enchanted maze or find yourself lost in a different dimension of magical challenges? The journey unfolds in this mystical escape!
Solution
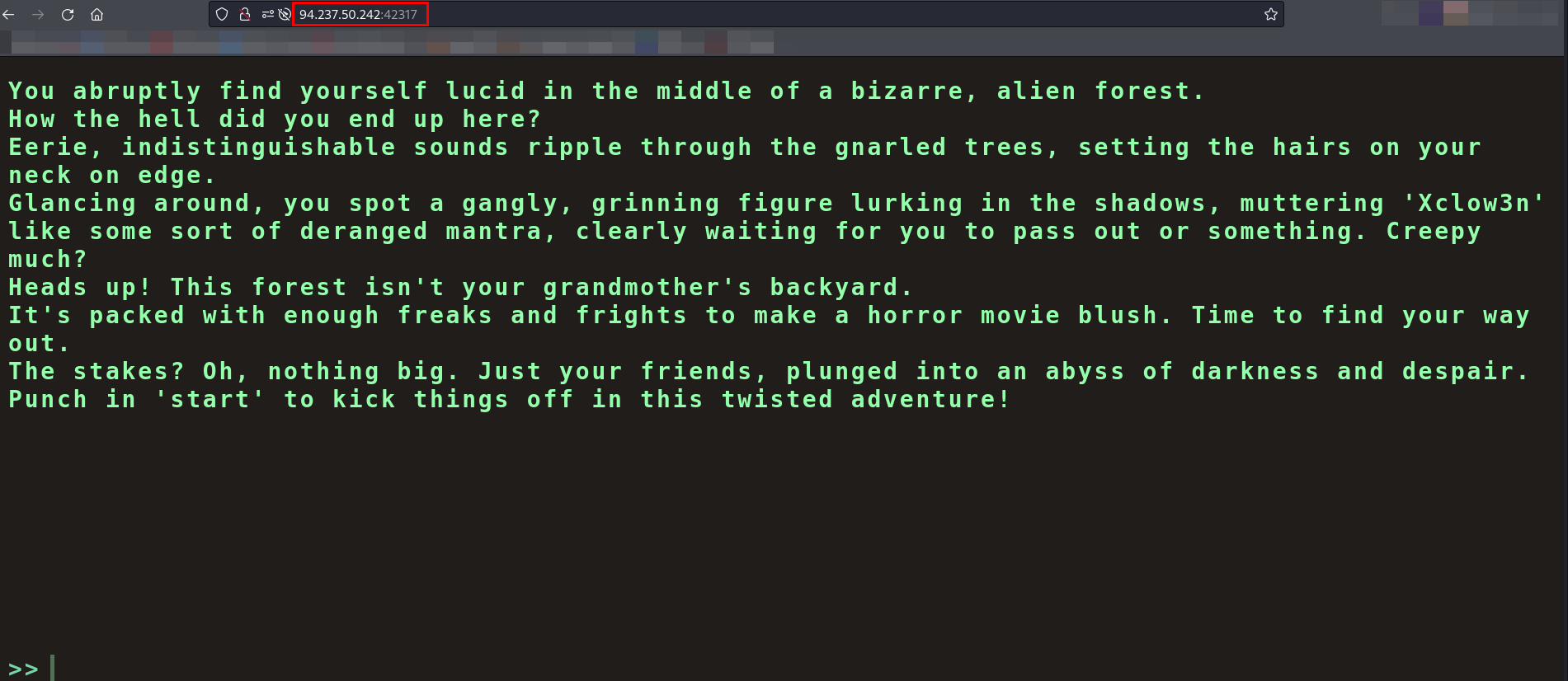
Since this is a web challenge, I began by browsing the target website provided.
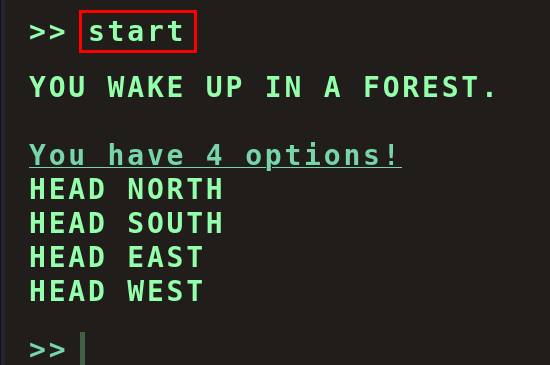
After selecting start, four choices appeared on the screen.
Without any clear indication of the right path, I took a gamble and chose HEAD NORTH.
This led to another set of four options. Relying on trial and error, I managed to advance through three stages: HEAD NORTH → FOLLOW A MYSTERIOUS PATH → SET UP CAMP.
But when I reached the fourth stage, none of the available choices worked. No matter what I selected, the result was always the same - Game Over.
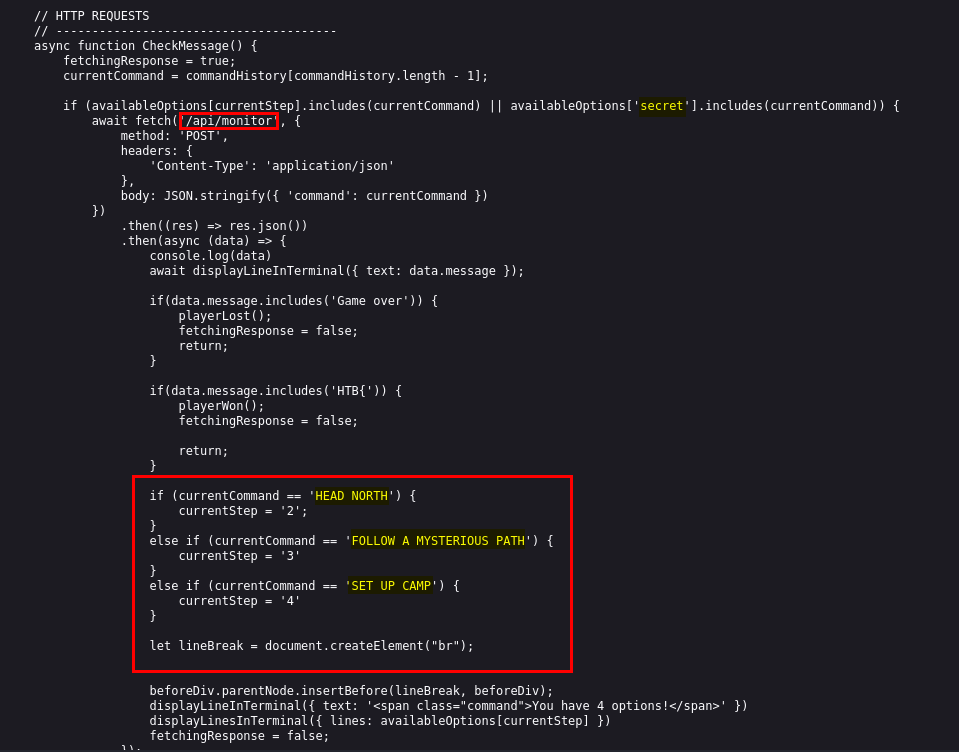
While checking the page source, I came across three .js files (commands.js, game.js and main.js).
In main.js, I observed that an API (/api/monitor) was being used to retrieve a secret upon selecting the correct options.
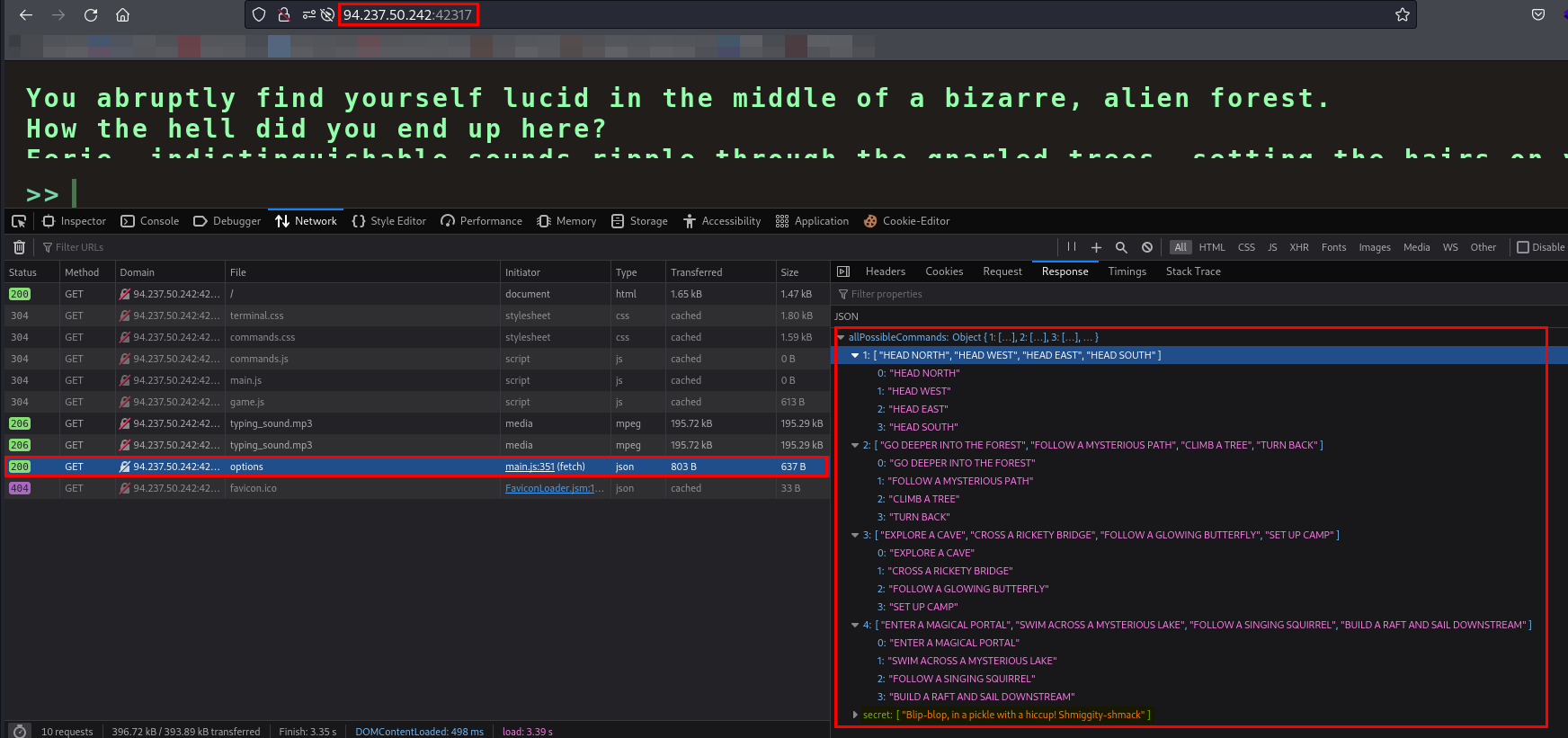
By analyzing the source code, I found the correct answers for the first three stages, but the fourth one remained unclear. So, I decided to check the Network tab in DevTools to see what resources were being requested. I found /api/options which was showing all the possible commands.
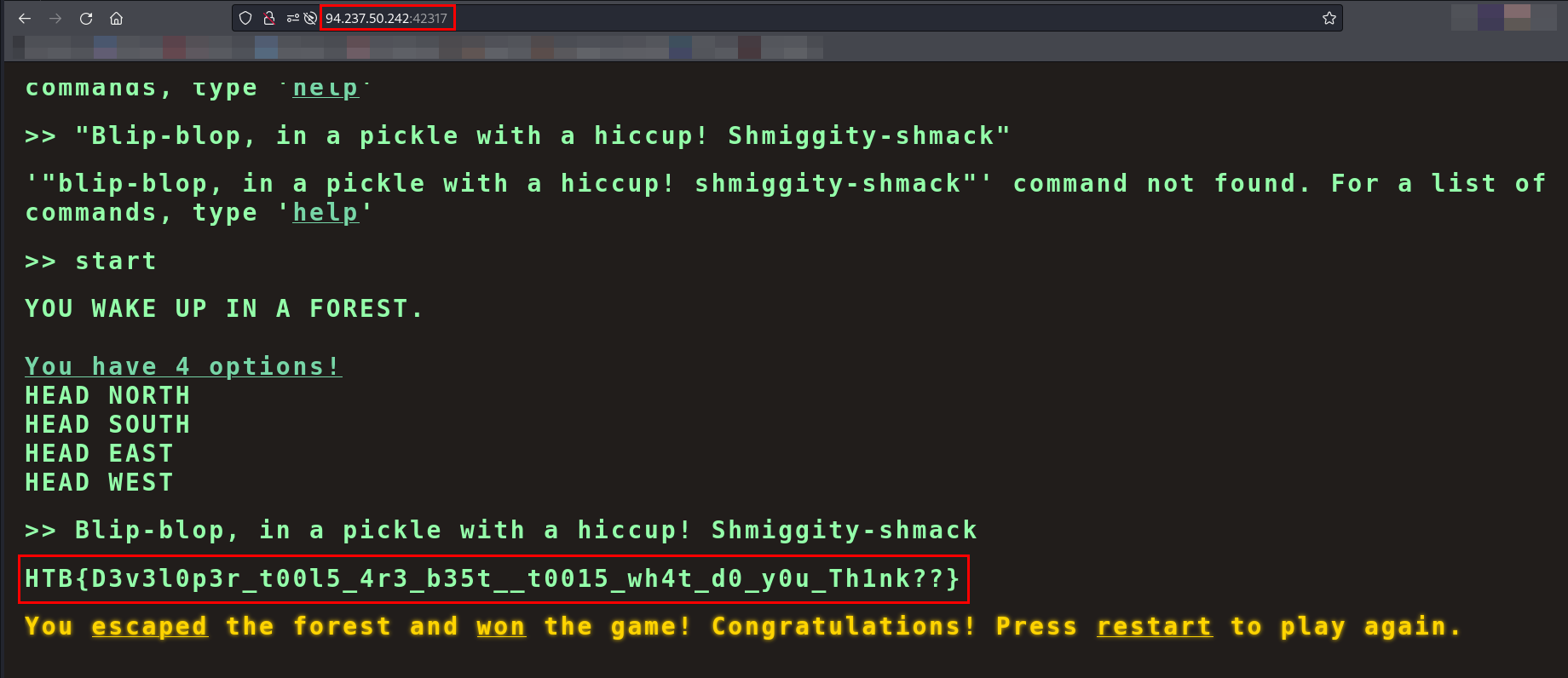
I found the value of secret so I have used the value of secret as a command and I found the flag.
Flag -
1
HTB{D3v3l0p3r_t00l5_4r3_b35t__t0015_wh4t_d0_y0u_Th1nk??}
Thanks for reading this far. If you enjoyed the writeup, do support me here.